Connect one org
A customer admin authorizes a Salesforce org.
Admins publish a bounded assistant surface. Users get named access to one assistant at a time. If that sounds narrower than most AI tools, that is the point.
This page is intentionally plain. We would rather be specific than sound impressive.
Assistant-scoped endpoint. Bounded surface. Named-user runtime.
Evaluating the protocol side? Read the Salesforce MCP overview.
A customer admin authorizes a Salesforce org.
The assistant gets a defined data surface and tool set.
Assistant access is granted deliberately, not implied.
Each session resolves to tenant, org, user, and assistant.
The access boundary is the published assistant surface and the assistant-specific runtime endpoint, not a generic whole-org connector. Preview, release review, session binding, and audit logging are part of the product model, not extras layered on later.
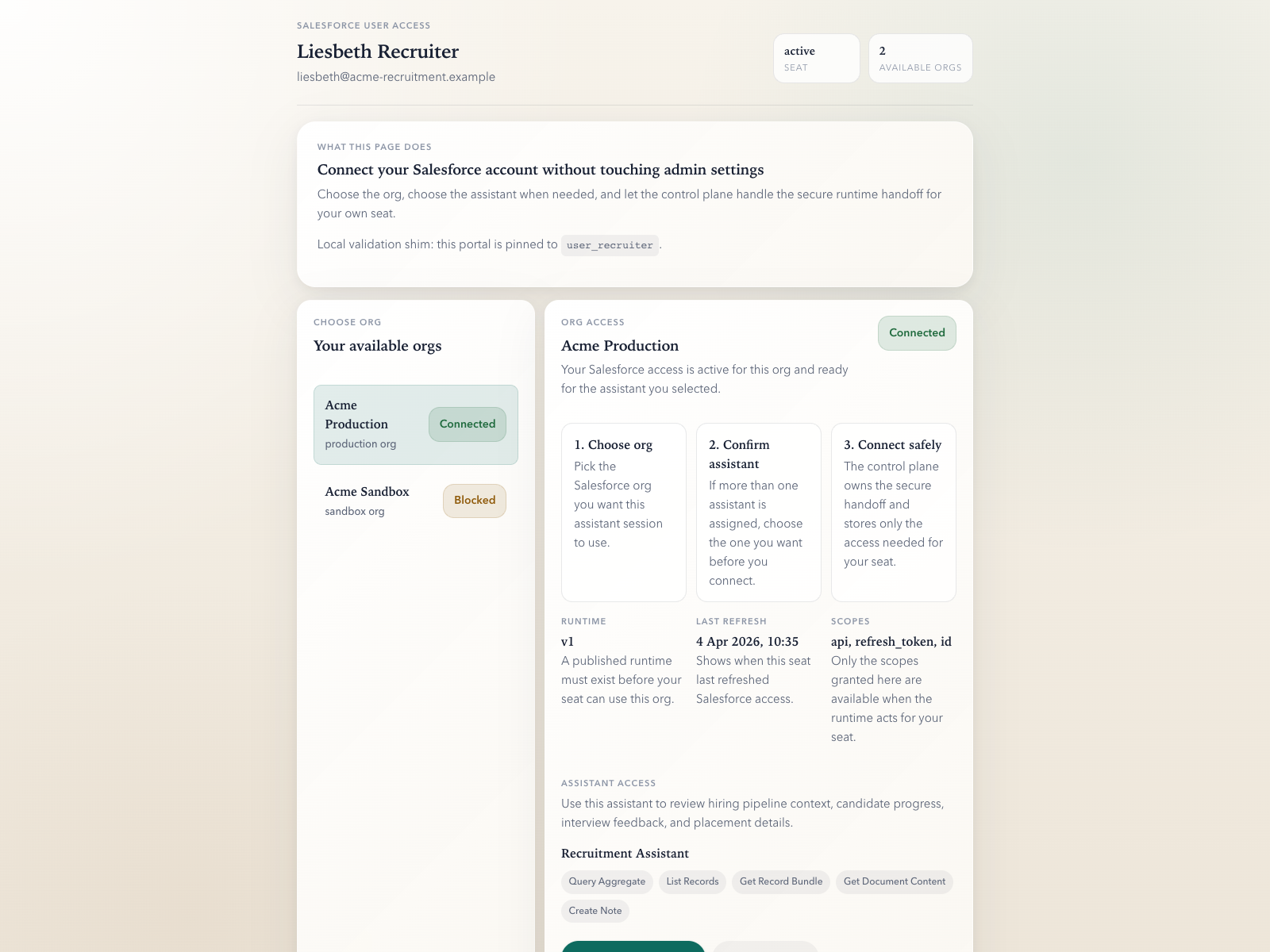
The admin chooses what an assistant can read object by object and field by field.
Published assistants get their own runtime endpoint instead of sharing one catch-all MCP connector.
Users receive assistant access explicitly instead of inheriting broad workspace access.
Assistant invocations record runtime metadata with tenant, org, user, assistant, tool, timing, and outcome.
| Capability | Status | Current posture |
|---|---|---|
| Invocation log per user | Partial | Runtime events exist with tenant, org, user, assistant, tool, timing, and status. The polished customer-facing console does not yet. |
| Record / field provenance | Partial | Tool and action shape are captured today. Full customer-facing provenance is not. |
| External agent-platform identity attribution | Partial | emcee can bind tenant, org, user, and assistant when it owns the runtime session. Shared third-party agent connections should be treated as shared identity until provenance is surfaced explicitly end to end. |
| Compliance export | Not yet | Planned for GA rather than rushed into early access. |
europe-west1 today.We would rather answer a direct security or architecture question than hide behind a demo flow. If the current posture is too early for your process, say so. That is useful information.