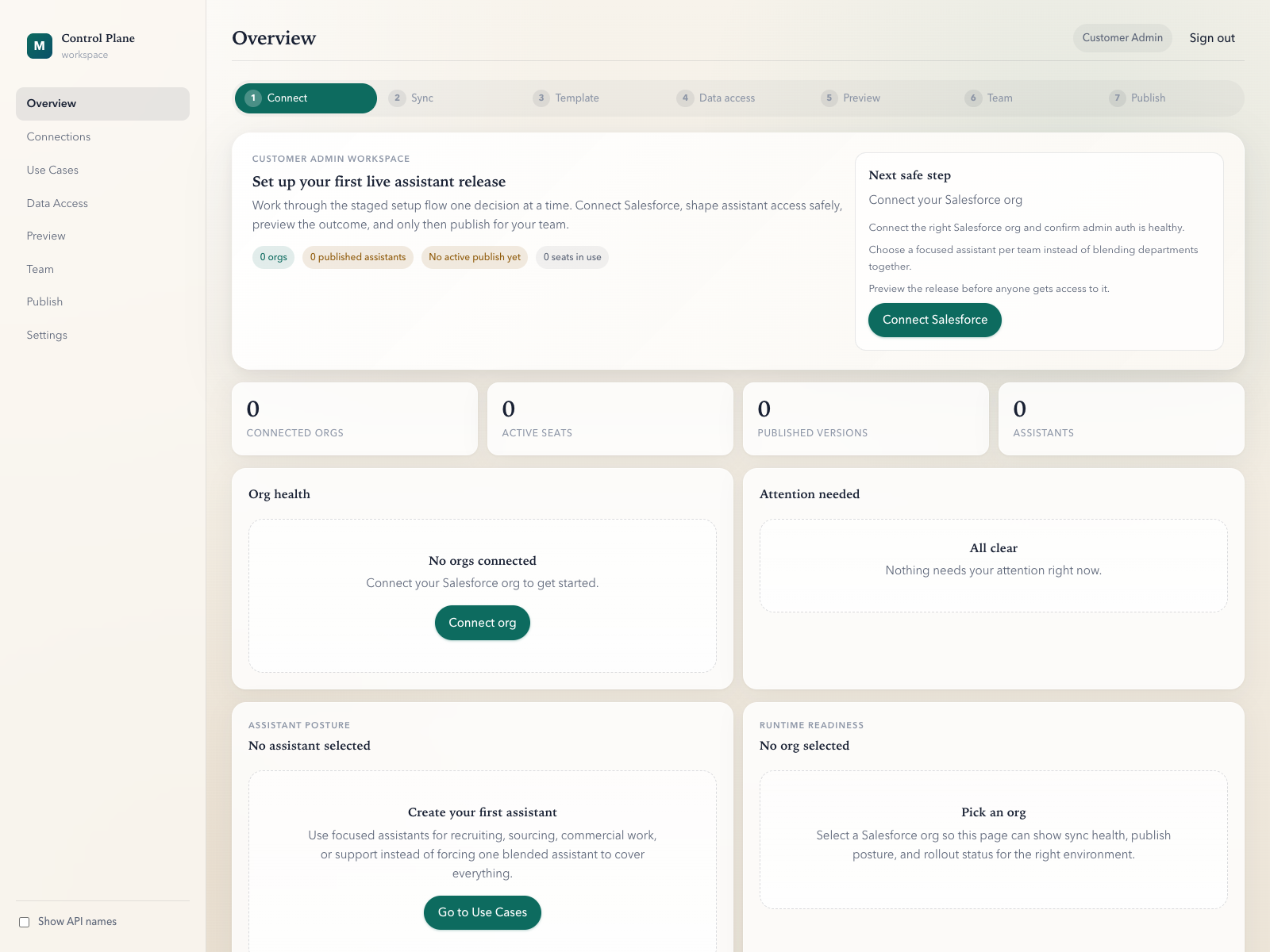
1. Connect Salesforce org.
Start from the system the team already works in. Do not export data into a separate AI silo.
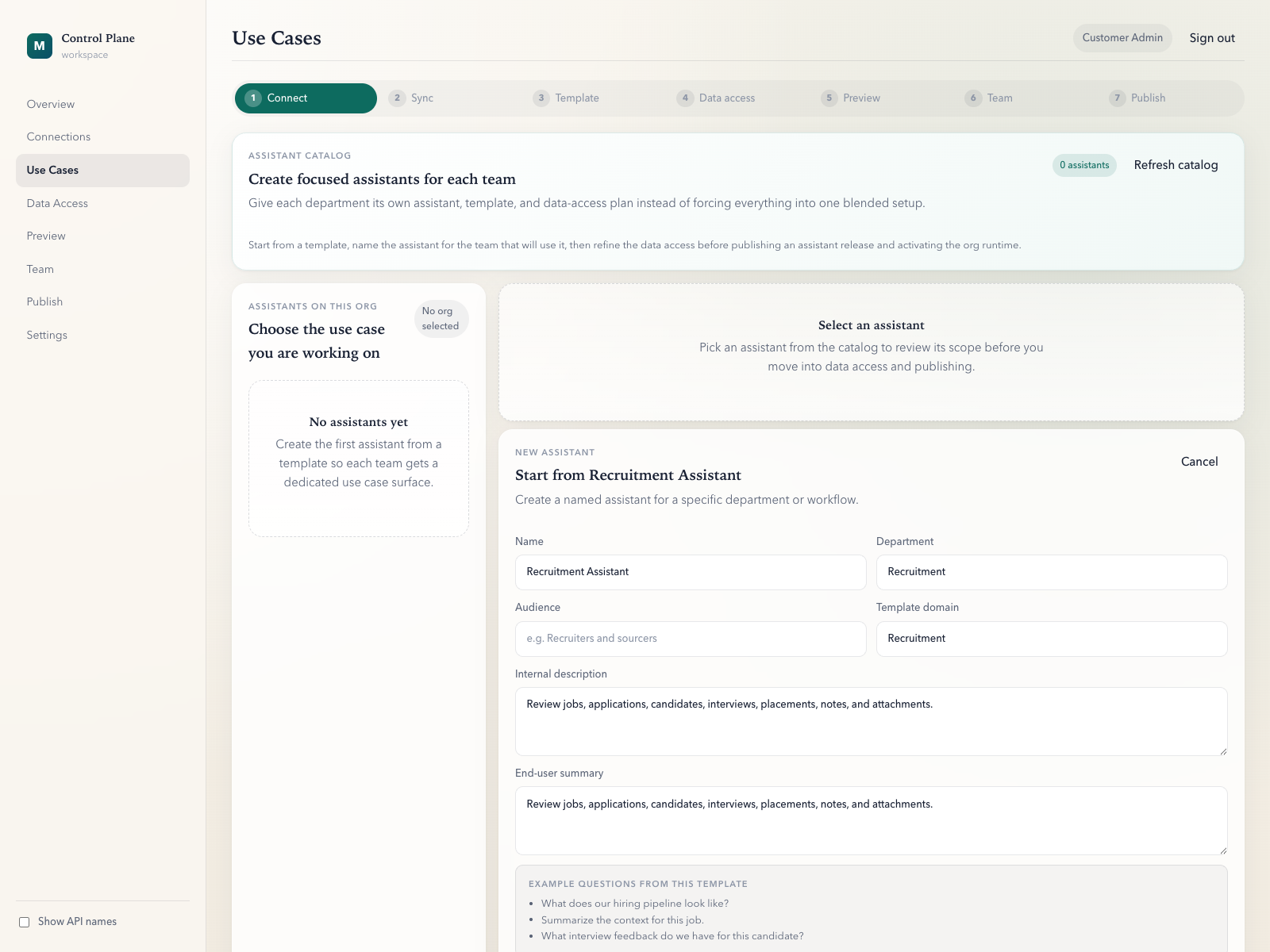
2. Publish bounded assistants per workflow.
Choose the objects, fields, bundles, and tools that assistant is allowed to use. If it was not published, it is out of bounds.
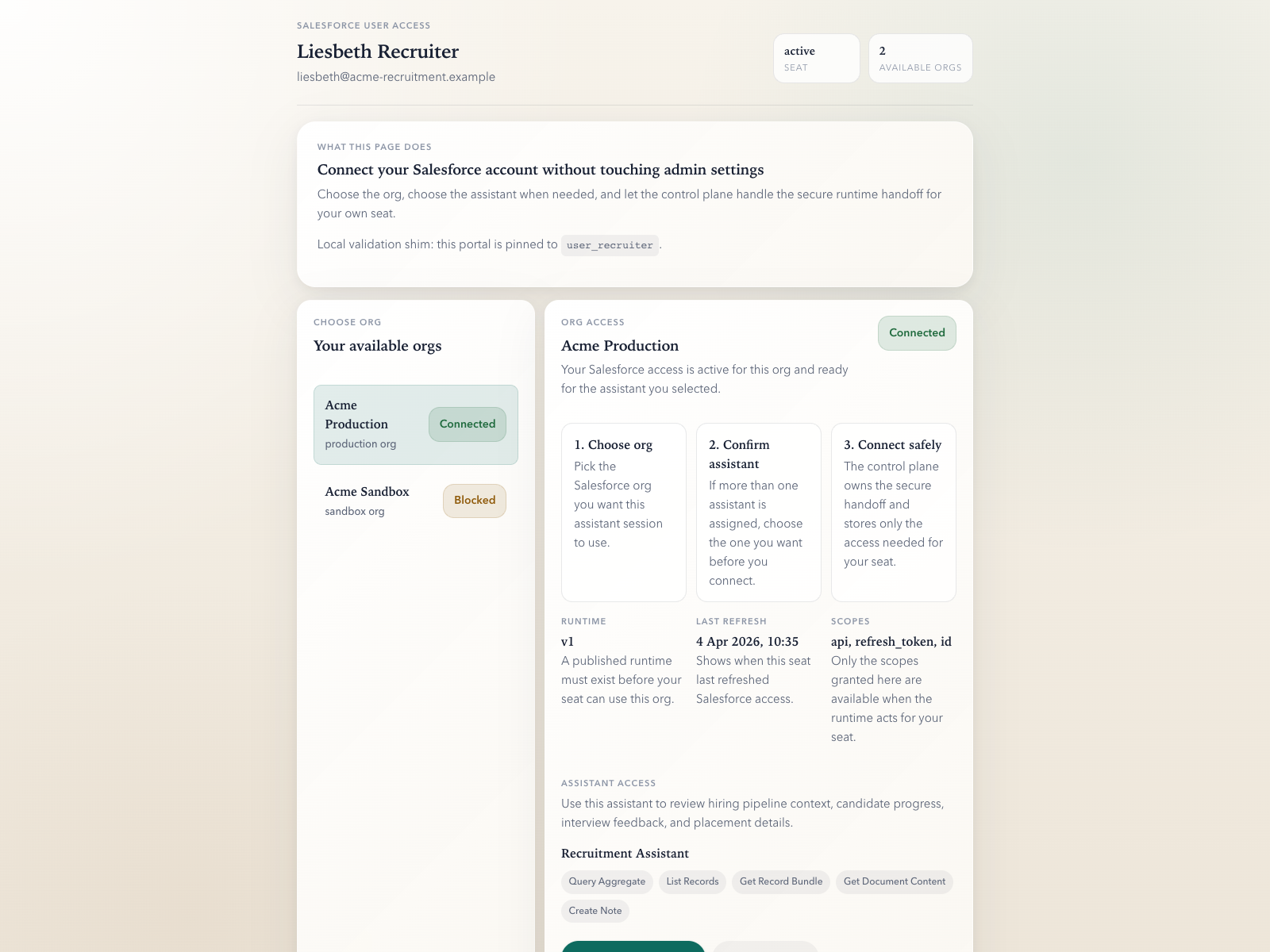
3. Assign it to named users.
Users receive assistant access explicitly. Runtime sessions resolve to one org and one assistant at a time.